Most job interviews ask the question "What is your biggest weakness". Some can give answers that aren't really weaknesses at all, but reworded strengths to get around answering the actual question. After working not only in infosec, but the technology industry for so long, I know exactly what my biggest weakness is. For the most part I can not speak in absolutes (see what I did there). I can't tell a customer "Yes our product will catch this ransomware", "Our customer service will handle your case this way each time", or "This blinky box will fix this issue". The only way I can speak in absolutes is when I have all of the data from a specific incident and can prove that it would happen with hard facts. Science yo.
Part of me thinks that this behavior is one of the larger results of my lack of self confidence in what I do day to day. The other part of me stands firm and says "No, that's bullshit. You don't KNOW for a fact that it will do X, because you don't have all of the data. Telling the customer that is being honest and not blowing smoke up their asses". We all constantly have Sales Engineers giving us flashy sales presentations on how their tech is the best in the market and always been, while we attempt to disseminate the actual technology from the sales and marketing pitch.
I've always been trusted by my peers and leadership to offer up point blank and blunt honesty when asked. I've given that on interviews as my biggest weakness before. Honestly it can be a weakness and not speaking in absolutes is a subsection of that. I'm not going to tell you a lie to make our company or myself look any better than we are in reality. I've turned down some amazing career opportunities due to the lack of confidence I have in a company or product. I knew that I wouldn't be right for the role because I'd have to bullshit my way around the true facts of the technology too often. Giving the answer of "I can be too honest sometimes." in an interview can steer the conversation in a few ways. I've been asked to give an example of times when I was too honest and it bit me in the ass. Actually that doesn't happen extremely often, but it can rub people the wrong way or make them think I'm not as good at what I do as the next person. I may or may not be better than the next person, but at least you'll know what I'm telling you isn't sugar coated.
I'd like to think I'm not too harsh or a ballbuster when stating the facts, but I do know that I can come off like that to certain personality types. I've been told to speak in absolutes for everything before, and the first time I've felt comfortable doing so is when writing my book. The reason? Because I've researched the hell out of every piece of it. My biggest fear is letting other's down or misinforming someone that is reading it. I am able to speak authoritatively because I've had the time to do the research and come up with enough information to put it forth in the writing. This is something I constantly struggle with, as well as overwhelming self doubt on a regular basis, but continue to work on daily.
Either as a customer or practitioner, where do you stand on the matter? If you're paying for a service or looking to get a service, do you have red flags that appear when someone guarantees you a product will do something? I think in this day and age you should. Every piece and part of our moving industry changes daily, there isn't a piece of software or hardware out there that is guaranteed to work 100% of the time. When there is a 100% is when I'll be comfortable phrasing sentences with "This WILL" or "EVERY TIME".
Thursday, August 11, 2016
Wednesday, July 20, 2016
Security for the Masses
Not long ago I was talking to my mom a little about what I do. I explained to her the intricacies of implementing solutions, securing large organizations, and some of the overall struggles we face day to day. After this conversation she came to me and said that I should write something about how the average person should be mindful and protect themselves day to day on the internet and on their computers. While this won’t be super technical content, I do hope that it will be an article you can share with your family members, friends, and coworkers on how to better keep themselves protected.
This is going to be a sort of laundry list of ways that the average computer user can better secure their life day to day. Being in the information security industry, I see super scary hacks and ways that bad attackers can take advantage of everyone. While I won’t go into what all of the scary things are, I’ll list the top 5 categories that will give the biggest bang for your buck.
I hope that all of the above tips can be something that you would handout to the circle of people that you know. Security is everyone’s responsibility and the more we all work towards a common goal, the safer we all become!
This is going to be a sort of laundry list of ways that the average computer user can better secure their life day to day. Being in the information security industry, I see super scary hacks and ways that bad attackers can take advantage of everyone. While I won’t go into what all of the scary things are, I’ll list the top 5 categories that will give the biggest bang for your buck.
Password Security
-
Password security can be difficult depending on how you handle it. You have a hundred things that you need to use passwords for, there is no way that you’ll be able to remember them all, right? Wrong! That’s something that we all have to deal with in this day and age. There is a type of software called a password manager that you can install. This software will allow you to have a strong, unique password for each website or service that you use, without you having to remember it. It is securely stored in the application, and the only password you will need to remember, is for the application itself. A few reputable password managers include, KeePass, LastPass, PasswordSafe, and 1Password.
You also should remember not to trust others with your password. Not only people, but never ever save your passwords in your internet browser. It is very easy for malware or viruses to steal that information.
Since you’ll be using a password manager now, make sure your passwords are strong. An 8 character password will take anywhere from 30 seconds to 24 hours to crack with a free piece of software from the internet. At least for your important accounts (banking, amazon, ebay, paypal, anything connected to something money related) you should use a 10 character passphrase. Doing this correctly will make your password almost impossible to crack. One way of making secure passwords easier to remember is using phrases from books, songs, expressions, etc, and substituting characters. The phrase
“You Are My Sunshine” == You@reMySunsh!n3.
Enable Multi-Factor Authentication/MFA (or Two-Factor Authentication/2FA) on sensitive accounts
-
2FA takes your login and password for a website or service and gives you a very high increase in protection. Many banks provide it as an option, as well as Facebook, Twitter, other popular social media accounts, Gmail, etc. 2FA adds another step in the form of a PIN or code to your login process by either texting it to your cell phone, emailing it, using an application such as Google Authenticator or Duo Security, or a physical device such as a key fob or token generator.
On the website https://twofactorauth.org/ you can search for services and it will list who does and doesn’t offer it as a service. More than likely you will be able to find your 2FA setup in your account security properties on each individual site.
Learn to be suspicious
-
You should be suspicious of any email, link, popup, or phone call that tries to create a sense of urgency. There are scammers out there everywhere. Many times they try to specifically target residents of retirement villages, but most will try their tactics on anyone. They come in many forms and here are a few:
- A fake email (called phishing) that may look exactly like a service that you use. These emails are very easily created and are attempting to direct you to a malicious website or infect your computer. If you have concerns from an email, never click on a link directly in it. Instead open up the website in a browser and type in the address manually. If there is any problem with your account you can either find it there, or call the company directly.
- A pop-up telling you that you have a virus or system slowness, and clicking *here* will fix everything. Do not click on it! It’s a malicious ad or pop-up on a potentially infected website that is trying to spread the infection or steal your information.
- A phone call from “Microsoft”, ”Dell”, or another well known company asking for access to your computer. No one, ever, at any point in time, will call you at home to request access to your computer or information from you. If at any point in time you believe that it is a legitimate request, get their name and call back number. Don’t actually call them back at that number, but look up the service that you use, whether it be financial, medical, or otherwise and call that number instead to inquire about your possible account issues.
Perform Routine Maintenance
-
Perform routine maintenance, such as updating your anti-virus (don’t let the renewal pass), and running anti-malware software monthly. There are several anti-spyware and anti-malware companies that are reputable. Download the software directly from their website and not from an ad elsewhere. www.Malwarebytes.org is a great piece of software that will find and remove security risks from your computer. Update and run Malwarebytes once a month, and remove everything it finds. There is a free and paid version.
More than likely you are running a Microsoft Operating system of some type. You should always apply updates monthly. There are going to be many other pieces of software on your computer that you should keep up to date as well. Things like Adobe Reader, Firefox, Chrome, etc that will have constant security bugs that need fixed. A free piece of software called Secunia (www.secunia.com) will let you know what pieces of software are vulnerable to an attacker. Also, please, if you’re reading this and have Windows XP you need to do everything in your power to get onto a newer operating system. Just trust me.
Protect your browsing
- Use a web browser other than Internet Explorer (IE). www.google.com/chrome or www.getfirefox.com are both exceptional browsers that have the ability to be more secure than the default IE.
- Install extensions on your new browser. Two extensions specifically, one named Ad-blockerPlus and another called No-Script, will turn off a large portion of very bad things displayed on websites.
I hope that all of the above tips can be something that you would handout to the circle of people that you know. Security is everyone’s responsibility and the more we all work towards a common goal, the safer we all become!
Wednesday, May 25, 2016
Getting your foot into the infosec door
Time and time again I have the discussion with my peers about mentoring and a starting a career in infosec. I’ve been asked my opinion, what I’ve personally done, and what others can do to be successful. Recently there was a panel discussion held on the subject of infosec careers at a Michigan Security group called #MiSec. It covered a large range of information such as mentoring, networking, contributing, and attitude. For a good write up on the session itself you can visit https://blog.greenjam94.me/path-dark-side/.
It is said that the lazier the tech worker, the harder they work to automate tasks. My goal is to put down my thoughts in this article to point others to for a beginner guide of my recommendations. While it’s only driven by my personal experience and observations, it seems valuable to enough people to warrant it’s own automation.
So a fast primer on how I got here. Like most people I wasn’t born into information security. I’m what you would consider a late bloomer to technology compared to most. I had plans on joining the Marines and when that didn’t pan out for personal reasons I thought to myself “Hey I’m decent with computers, I’ll do that!”. I didn’t have my first tech job until I was almost out of college. I had gone for my 2 year “Helpdesk” degree at a local tech college and honestly had no idea what I had just learned or how to apply any of it to the real world. After 5 years at various helpdesks and another 5 as a network/systems admin I was finally introduced into the world of infosec. I had no idea that it was an entire subculture.
My first toe step into infosec had come from a project that a friend had gotten me involved in. Being an overachiever, I had jumped in right away and started to work on this project. Bi-monthly skype meetings, shared documents, collaborating with people I barely knew. I was loving it! Shortly after that the project owner killed it but I had already started the ball rolling in my mind. I knew that I wanted to be a part of more than just a 8-5 job. I cared immensely for the work I was doing day to day and I wanted to continue and expand upon that to help out as many people as I could. Even being involved in a project that didn’t go anywhere gave me the drive and experience I needed to realize that there was so much more out there that I could be involved in. So that is my first piece of advice. Find or create a project. It doesn’t matter what your skillset is, there *will* be a project out there that needs help. Documentation is needed on 99% or more of the open source projects out there. If you’re good at scripting or programming find a need and fill it. It may help you in your day to day job, or maybe it’s just a fun project that you do on the side. Either way you are spending your time on something useful that could end up helping save time for someone.
My second piece of advice is volunteer and participate at an information security conference and attend local meetups. There are hundreds of them across the US and they almost always need volunteers. Just attending a conference has it’s benefits, but truly immersing yourself will push you further to learn and experience more. Maybe you saw someone give a talk or training on something or overheard an interesting conversation. Many careers have been started by having a simple conversation about a passion over lunch or a beer. Remember those projects that I talked about working on before…...a great ice breaker. Networking is a game changer in our industry. I’m not saying that it’s the silver bullet for everyone. You can network all you want, but unless you are a desirable candidate it won’t matter. Having a willingness and desire to learn, listen, collaborate, and the ability to think for yourself are all ideal traits in such a fast paced industry. Others will want to work with you if you are a positive person that they can rely on and trust. You can also join a team for a capture the flag (CTF) or other competition, attend training, or maybe even create your own event. CTFs are a great way to challenge yourself and build problem solving skills. You can learn by watching and competing with others.
Another item to add to your “to-do” list should be to either find or be a mentor. Mentorship can come in many forms but is not just going to be solutions and information handed to you on a silver platter. If someone is offering to mentor you, they are doing it for free with their extra time, so don’t screw it up. Remember, they don’t owe you anything. Mentoring can be extremely rewarding for both parties and also can occupy a lot of time depending on the level of commitment. Try to find someone in a different company so you can bounce ideas off of each other from different perspectives. You don’t have to have a strict career path to be mentored. With so much information in infosec having a broad understanding of any piece of it will help you down the road.
While a career in information security could be an 8-5 job, to excel in it won’t be. I think it’s safe to say any career can be made into an 8-5 without personal and professional drive and commitment. You are going to get a return on investment only on the work that you put into it.
It is said that the lazier the tech worker, the harder they work to automate tasks. My goal is to put down my thoughts in this article to point others to for a beginner guide of my recommendations. While it’s only driven by my personal experience and observations, it seems valuable to enough people to warrant it’s own automation.
So a fast primer on how I got here. Like most people I wasn’t born into information security. I’m what you would consider a late bloomer to technology compared to most. I had plans on joining the Marines and when that didn’t pan out for personal reasons I thought to myself “Hey I’m decent with computers, I’ll do that!”. I didn’t have my first tech job until I was almost out of college. I had gone for my 2 year “Helpdesk” degree at a local tech college and honestly had no idea what I had just learned or how to apply any of it to the real world. After 5 years at various helpdesks and another 5 as a network/systems admin I was finally introduced into the world of infosec. I had no idea that it was an entire subculture.
My first toe step into infosec had come from a project that a friend had gotten me involved in. Being an overachiever, I had jumped in right away and started to work on this project. Bi-monthly skype meetings, shared documents, collaborating with people I barely knew. I was loving it! Shortly after that the project owner killed it but I had already started the ball rolling in my mind. I knew that I wanted to be a part of more than just a 8-5 job. I cared immensely for the work I was doing day to day and I wanted to continue and expand upon that to help out as many people as I could. Even being involved in a project that didn’t go anywhere gave me the drive and experience I needed to realize that there was so much more out there that I could be involved in. So that is my first piece of advice. Find or create a project. It doesn’t matter what your skillset is, there *will* be a project out there that needs help. Documentation is needed on 99% or more of the open source projects out there. If you’re good at scripting or programming find a need and fill it. It may help you in your day to day job, or maybe it’s just a fun project that you do on the side. Either way you are spending your time on something useful that could end up helping save time for someone.
My second piece of advice is volunteer and participate at an information security conference and attend local meetups. There are hundreds of them across the US and they almost always need volunteers. Just attending a conference has it’s benefits, but truly immersing yourself will push you further to learn and experience more. Maybe you saw someone give a talk or training on something or overheard an interesting conversation. Many careers have been started by having a simple conversation about a passion over lunch or a beer. Remember those projects that I talked about working on before…...a great ice breaker. Networking is a game changer in our industry. I’m not saying that it’s the silver bullet for everyone. You can network all you want, but unless you are a desirable candidate it won’t matter. Having a willingness and desire to learn, listen, collaborate, and the ability to think for yourself are all ideal traits in such a fast paced industry. Others will want to work with you if you are a positive person that they can rely on and trust. You can also join a team for a capture the flag (CTF) or other competition, attend training, or maybe even create your own event. CTFs are a great way to challenge yourself and build problem solving skills. You can learn by watching and competing with others.
Another item to add to your “to-do” list should be to either find or be a mentor. Mentorship can come in many forms but is not just going to be solutions and information handed to you on a silver platter. If someone is offering to mentor you, they are doing it for free with their extra time, so don’t screw it up. Remember, they don’t owe you anything. Mentoring can be extremely rewarding for both parties and also can occupy a lot of time depending on the level of commitment. Try to find someone in a different company so you can bounce ideas off of each other from different perspectives. You don’t have to have a strict career path to be mentored. With so much information in infosec having a broad understanding of any piece of it will help you down the road.
While a career in information security could be an 8-5 job, to excel in it won’t be. I think it’s safe to say any career can be made into an 8-5 without personal and professional drive and commitment. You are going to get a return on investment only on the work that you put into it.
Wednesday, January 20, 2016
Information Security Podcast List
Some of my favorites:
southern fried security (http://www.southernfriedsecurity.com/) w/ Steve Ragan
brakeing down security (http://www.brakeingsecurity.com/) w/ Bryan Brake
Down the Security Rabbit Hole (http://podcast.wh1t3rabbit.net/) w/ Rafal Los
Defensive sec (http://www.defensivesecurity.org/) w/ Andrew Kalat and Jerry Bell
Hurricane labs (https://hurricanelabs.com/podcasts/) (obviously have to put this here) with Bill Mathews, Kelsey Clark, and other awesome people I work with
PVC sec (http://www.pvcsec.com/) w/ Edgar Rojas
TrustedSec, LLC podcast (https://www.trustedsec.com/podcast/) w/ lots of their awesome people
southern fried security (http://www.southernfriedsecurity.com/) w/ Steve Ragan
brakeing down security (http://www.brakeingsecurity.com/) w/ Bryan Brake
Down the Security Rabbit Hole (http://podcast.wh1t3rabbit.net/) w/ Rafal Los
Defensive sec (http://www.defensivesecurity.org/) w/ Andrew Kalat and Jerry Bell
Hurricane labs (https://hurricanelabs.com/podcasts/) (obviously have to put this here) with Bill Mathews, Kelsey Clark, and other awesome people I work with
PVC sec (http://www.pvcsec.com/) w/ Edgar Rojas
TrustedSec, LLC podcast (https://www.trustedsec.com/podcast/) w/ lots of their awesome people
Monday, December 28, 2015
RUCTFE and why a CTF can benefit your organizational security.
I had the great honor of being the defensive (blue) team captain for the RUCTF, a technical capture the flag event organized by a group of security professionals located in Russia. I enjoy being able to lead and teach others, learn new tactics, and be a part of a competitive team. Misec (www.michsec.org) is a collection of Michigan (and in my case, Northern Ohio) based security professionals that meet regularly to learn, compete, and socialize in different ways. In this article I have a co-author that has written about his first CTF experience. James Green is a senior at Michigan State University in East Lansing, Michigan. After you read about his experience I’ll go over why challenges of this nature can benefit your organization.
First off, it is a capture the flag! Why am I so pumped about a game of capture the flag? It is the international hacker version of capture the flag!! Imagine this, Russia is the host and they give every team a virtual machine (vm) with a number of applications “ready” to be deployed. Each team is responsible for keeping their applications online as well trying to bring down other teams. Our Russian hosts have access to everyone’s vm and are able to “drop” flags throughout them. Flags are strings like “A23HFK36JG732IE436GHD8OVH1297QUF=” and you know it’s a flag because it’s 32 capital letters and numbers followed by a “=”. Each app has a unique twist that makes the game more interesting. For example, one was written in Python, another was in C and used .cgi files. Some stored data in mysql and sqllite databases, others used files with JSON. The variety added complexity that made the game more fun. Misec arranged people into four groups. Red team focused on attacking other teams and searching for flags. Blue team was responsible for defending our applications and hardening the security of the server. Green team was operations, they built and maintained the network. Fuchsia team were our developers and became jack of all trades because they worked alongside red team on code dives while implementing blue team’s defenses.
I was a part of the red team. I really enjoy penetration testing and I knew this would be great experience. Our team lead was Austen, and he walked me through a lot of what it means to be on the read team. I’m very thankful for his help. Last weekend was a prep meeting and I found out that my old Kali box wouldn’t update, so I had to prepare a new one during the week. #Misec was really helpful every time that I got stuck or hard a question during setup.
My day started at 3:30am with a blaring alarm clock. That was probably the worst part of the day, which also means the day would only get better right? I arrived on site around 4:20, just in time to help hang wires and bring in equipment. As everyone showed up, we brought out our machines, connected everything and got the VMs ready. I worked with Brad (Fuchsia lead) and Austen to reset the root password and config SSH so that I could log in from Kali. Once our environments were set up, the red team started looking for what ports were open and what services were listening. This was the first time we found what the apps were using. Like I said earlier in the explanation, there was a wide range of databases and languages at our disposal. Brad dumped the databases and passed it around for others to try and understand while Amanda (Blue lead) searched for passwords and configurations that needed to be updated. Otherwise other teams could use the default accounts to hack into our VM.
Throughout the morning, the green team worked to get the network online. As they did that, the red and fuchsia teams searched high and low for vulnerabilities in our VMs that would get us an advantage against other teams. The blue team continued to check and secure them as needed. I spent this time running my VM through Armitage. I wasn’t able to find any exploits right away that the apps were vulnerable to, but that was to be expected. Armitage is very automated and it’s hard to customize exploits to work with specific apps. After that turned out to be unsuccessful I turned my attention towards Burp Suite. However, I wasn’t able to configure it correctly so I turned my attention towards code dives hoping to find something obvious like SQL injection or worse. The apps were all in their own directories under home/ and it was very interesting to look through how our hosts had made the VM. As I was looking around, Austen found one of the apps used the same auth token in a cookie for every user in the app. I helped him confirm that by recreating what he did on my VM. The idea for a exploit was that if we could pick up a player’s cookies when they dropped flags off to the host, we could get into the apps they were just at. Austen also found a second vulnerability where for the Python app, the password was “hashed” by turning numbers into their ascii hex equivalent. I wrote a small python script to decode the hashes incase we ever got a hold of another team’s JSON files. Just a quick note, this is the first script I’ve written to help break a web app and I was really excited to see how easy it seemed; the development background (and wide range of python libraries) really helped.
Between 11 and noon, the green team was able to bring our network online at full capacity. This was our first time being able to score points and everyone was really excited. However this also brought a new issue, where other teams could now attack us. The plan seems to be working pretty well though, we were earning points for keeping the app alive and no one seemed to be trying to attack the server too badly from the outside. As soon as the red team had access to other teams, we started to poke other teams servers to see what was possible. I tried to find a way to get my python script to work, but first I needed a way to find the json file. I tried calling it directly from the URL, SSH-ing into their application server, and just crawling through the app. This didn’t turn out very well so I tried another tactic. Now that we had real targets, maybe it’d be worth trying Armitage again, other applications might not be as hardened as ours, right? Well, like my VM, it didn’t return any easy results, so I abandoned the idea to return to poking at random teams’ apps, hoping to find a XSS or SQL injection bug somewhere. While I was digging around, my box froze. I just rebooted Kali and continued my barrage of random attempts to attack other teams.
During my assault, Amanda came over to ask if we had done a game-wide nmap scan to list all of the active teams. The game was a almost 3/4 of the way done and no one on the red team had thought to scan everyone after we had gotten our apps up on the game network. Amanda showed me how to use RAWR, a python wrapper of nmap that allowed us to scan and log more cleanly than just saving nmap output straight to a text file. While Amanda filled me in, she was scanning some of the other teams’ servers. I used Python to create a input file for RAWR that would hit the production box for 254 ip addresses. As I started to run the scanner, Austen found another way to grab flags by recreating auth tokens for users of a Ruby app. He quickly wrote up a Ruby script to loop through different teams and a range of IDs both of which were used to create the auth tokens and distributed the code amongst the red team to try and crack as many teams as possible. He ran the code first and started to find flags on the other teams servers, however when he went to turn them in, the host’s scoreboard server was having connection issues.
Since there were issues from the host, we tried to hold onto flags until we were able to reconnect to the scoreboard and turn them in. This was risky because it was going on 2pm and the game was only live for another hour. As soon as Austen found a valid flag, the red team started running his script over different teams trying to get their apps to give up more flags. I made a couple modifications to his script on my box so that instead of going through 100 IDs on a team, then going to another team and so on, the script would ask me for what team to scan and wouldn’t iterate to a second team. I was able to use this modification to run a few scripts at once and try to grab as many flags as possible. As we were searching, we were able to find a good amount of flags. The second modification I was trying was to add inputs for the starting and ending IDs for the script. I couldn’t get it to work and didn’t know why until after the game ended when I asked Austen to look it over. I was still able to get 6 flags in the last ten minutes of the game and I was very excited to have contributed to increasing the team’s score. It felt amazing. At the end of the game, we were ranked 118th out of over 300 teams and I was proud to have helped and learned so much, especially since we climbed 3 ranks within the last few minutes!
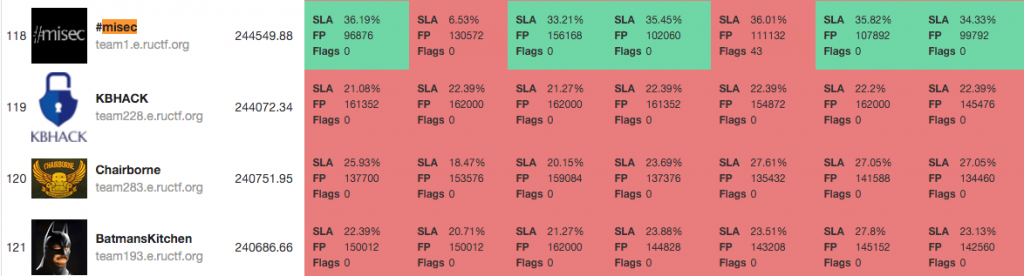
Misec beat Batman
I want to give a huge shout out to Misec for pooling some great local talent into an awesome team. Thanks to Steven for organizing this year’s event and to Jason for building our infrastructure/network. Also, if it wasn’t for Austen, Brad, Amanda, Wolf, Ben and everyone else who helped me and made me feel like a member of the team. I wouldn’t have been able to learn as much as I did or have as much fun without you. I can’t wait to see what will happen at ruCTFe 2016!
- James Green
As you can see, for the junior members of your organization or team members that want to learn new or improve upon existing skills, participating in CTF type challenges is invaluable experience. They are well crafted scenarios that can put you and your team in real life situations. Somewhere that you are able to practice both defensive and offensive skills and learn from a variety of people in different information security roles. Many companies don’t have the time or resources to create such elaborate scenarios for the practice that is needed for responding and handling real threats. The communication and technical skills gained from this practice will give you the upper hand no matter what role you play.
There are a variety of types of CTFs from jeopardy style where you submit certain answers (flags) for points, or in the case of RUCTFE it was an attack/defense design. If you are interested in participating you can contact a local security group or visit https://ctftime.org/ for a listing of some of the current ones that are out there. Whether you show up to organize, teach, learn, or spectate I can guarantee that you’ll leave having learned something new.
My First CTF: RUCTFE 2015 with #MISEC
What is ruCTFe?
First off, it is a capture the flag! Why am I so pumped about a game of capture the flag? It is the international hacker version of capture the flag!! Imagine this, Russia is the host and they give every team a virtual machine (vm) with a number of applications “ready” to be deployed. Each team is responsible for keeping their applications online as well trying to bring down other teams. Our Russian hosts have access to everyone’s vm and are able to “drop” flags throughout them. Flags are strings like “A23HFK36JG732IE436GHD8OVH1297QUF=” and you know it’s a flag because it’s 32 capital letters and numbers followed by a “=”. Each app has a unique twist that makes the game more interesting. For example, one was written in Python, another was in C and used .cgi files. Some stored data in mysql and sqllite databases, others used files with JSON. The variety added complexity that made the game more fun. Misec arranged people into four groups. Red team focused on attacking other teams and searching for flags. Blue team was responsible for defending our applications and hardening the security of the server. Green team was operations, they built and maintained the network. Fuchsia team were our developers and became jack of all trades because they worked alongside red team on code dives while implementing blue team’s defenses.I was a part of the red team. I really enjoy penetration testing and I knew this would be great experience. Our team lead was Austen, and he walked me through a lot of what it means to be on the read team. I’m very thankful for his help. Last weekend was a prep meeting and I found out that my old Kali box wouldn’t update, so I had to prepare a new one during the week. #Misec was really helpful every time that I got stuck or hard a question during setup.
Walk Through
Throughout the morning, the green team worked to get the network online. As they did that, the red and fuchsia teams searched high and low for vulnerabilities in our VMs that would get us an advantage against other teams. The blue team continued to check and secure them as needed. I spent this time running my VM through Armitage. I wasn’t able to find any exploits right away that the apps were vulnerable to, but that was to be expected. Armitage is very automated and it’s hard to customize exploits to work with specific apps. After that turned out to be unsuccessful I turned my attention towards Burp Suite. However, I wasn’t able to configure it correctly so I turned my attention towards code dives hoping to find something obvious like SQL injection or worse. The apps were all in their own directories under home/ and it was very interesting to look through how our hosts had made the VM. As I was looking around, Austen found one of the apps used the same auth token in a cookie for every user in the app. I helped him confirm that by recreating what he did on my VM. The idea for a exploit was that if we could pick up a player’s cookies when they dropped flags off to the host, we could get into the apps they were just at. Austen also found a second vulnerability where for the Python app, the password was “hashed” by turning numbers into their ascii hex equivalent. I wrote a small python script to decode the hashes incase we ever got a hold of another team’s JSON files. Just a quick note, this is the first script I’ve written to help break a web app and I was really excited to see how easy it seemed; the development background (and wide range of python libraries) really helped.
The apps go live
During my assault, Amanda came over to ask if we had done a game-wide nmap scan to list all of the active teams. The game was a almost 3/4 of the way done and no one on the red team had thought to scan everyone after we had gotten our apps up on the game network. Amanda showed me how to use RAWR, a python wrapper of nmap that allowed us to scan and log more cleanly than just saving nmap output straight to a text file. While Amanda filled me in, she was scanning some of the other teams’ servers. I used Python to create a input file for RAWR that would hit the production box for 254 ip addresses. As I started to run the scanner, Austen found another way to grab flags by recreating auth tokens for users of a Ruby app. He quickly wrote up a Ruby script to loop through different teams and a range of IDs both of which were used to create the auth tokens and distributed the code amongst the red team to try and crack as many teams as possible. He ran the code first and started to find flags on the other teams servers, however when he went to turn them in, the host’s scoreboard server was having connection issues.
Down to the wire
Misec beat Batman
Conclusion
- James Green
As you can see, for the junior members of your organization or team members that want to learn new or improve upon existing skills, participating in CTF type challenges is invaluable experience. They are well crafted scenarios that can put you and your team in real life situations. Somewhere that you are able to practice both defensive and offensive skills and learn from a variety of people in different information security roles. Many companies don’t have the time or resources to create such elaborate scenarios for the practice that is needed for responding and handling real threats. The communication and technical skills gained from this practice will give you the upper hand no matter what role you play.
There are a variety of types of CTFs from jeopardy style where you submit certain answers (flags) for points, or in the case of RUCTFE it was an attack/defense design. If you are interested in participating you can contact a local security group or visit https://ctftime.org/ for a listing of some of the current ones that are out there. Whether you show up to organize, teach, learn, or spectate I can guarantee that you’ll leave having learned something new.
Tuesday, September 22, 2015
Two-Factor Authentication: It’s not your mamma’s internet anymore.
The other day a friend of mine decided that it should be International Password Awareness Day.
This is an amazing idea!! It should be the start of a movement for better passwords everywhere! Sometimes however, I get ahead of myself and have to take a moment to step back. I then realize that for the most part password strength still won’t matter. Don’t get me wrong, with the passwords that we’ve seen in recent breaches or professional engagements, 99% of you need to go change your passwords right now (to a good one).
Even as much as I am into information security, I still have some bad habits when it comes to my personal passwords. I keep most of them in an encrypted password safe program, I don’t use dictionary words, keep them complex, don’t reuse them, and keep them over 12 characters. One of the practices that I don’t keep up with (as much as I should) is changing my passwords at a regular interval. Honestly it’s a huge pain. Sure if there is a big breach I’ll go and change my important account passwords. What ends up putting my mind somewhat at ease for a majority of my accounts is using services that allow you to take advantage of Two-Factor Authentication as a method to strengthen the login process.
Two-Factor Authentication (2FA) is a method of identifying individuals by using two separate methods. While the number of services and websites that provide 2FA is increasing, we rarely think about it in our own enterprise environments. There are a surprising amount of companies and services that decided to implement 2FA after a large scale or high visibility breach. Shown below is the widely known AP Twitter hack that brought the stock market down in April of 2013.
Amazingly Twitter started offering 2FA in August of that same year, less than four months later. While you can argue that this specific hack may still have been possible as it was proven to be a phishing attack, it’s also likely that 2FA could have prevented it as well.
Of course there are many ways that 2FA can fail to be the security blanket that we need, especially when it is implemented poorly. On top of doing your best to increase the complexity of your passwords it needs to be part of your defense in depth strategy and not just a bandaid for a compliance checkmark.
I’ll give you an example situation that I know for a fact has happened to several pentesters.
Company A decides that they want to implement 2FA by using the push notification or phone call method. A criminal or pentester comes along to break in by either phishing, using passwords from a recent breach, or a password brute forcing technique. Somehow they end up with a legitimate username/password combo, but they should be stopped from authenticating because of the 2FA right? Well in this case, the user gets the phone call or application alert that they have gotten so many times in the past. This notification doesn’t tell the user what they are supposedly logging into, so as a force of habit they acknowledge the alert or answer the phone call and press the # key. Boom the bad guy or pentester is in.
So the principle idea behind “Something you have” can take on different forms. In this situation it’s technically 2FA and allows Company A to be compliant but they are still not leveraging the security potential of the software. If they were to have that second form of authentication include a code as opposed to a single click or button, they would have been both secure AND compliant.
There are many other threats that I won’t get into right now. The bottom line is that passwords alone are weak, and adding 2FA strengthens that authentication method to be a deal more secure. In the words of Bruce Schneier:
“I am declaring today as International Password Awareness Day. After being in InfoSec for almost 20 years I have found that the single worst problem we have created is poor password hygiene. Not only do we make terrible passwords, we allow others to make even worse ones without holding them accountable. So let's all take a moment today to fix that. Change your password , ask your family, friends and coworkers to change theirs.” - Chris Nickerson
This is an amazing idea!! It should be the start of a movement for better passwords everywhere! Sometimes however, I get ahead of myself and have to take a moment to step back. I then realize that for the most part password strength still won’t matter. Don’t get me wrong, with the passwords that we’ve seen in recent breaches or professional engagements, 99% of you need to go change your passwords right now (to a good one).
Even as much as I am into information security, I still have some bad habits when it comes to my personal passwords. I keep most of them in an encrypted password safe program, I don’t use dictionary words, keep them complex, don’t reuse them, and keep them over 12 characters. One of the practices that I don’t keep up with (as much as I should) is changing my passwords at a regular interval. Honestly it’s a huge pain. Sure if there is a big breach I’ll go and change my important account passwords. What ends up putting my mind somewhat at ease for a majority of my accounts is using services that allow you to take advantage of Two-Factor Authentication as a method to strengthen the login process.
Two-Factor Authentication (2FA) is a method of identifying individuals by using two separate methods. While the number of services and websites that provide 2FA is increasing, we rarely think about it in our own enterprise environments. There are a surprising amount of companies and services that decided to implement 2FA after a large scale or high visibility breach. Shown below is the widely known AP Twitter hack that brought the stock market down in April of 2013.
Amazingly Twitter started offering 2FA in August of that same year, less than four months later. While you can argue that this specific hack may still have been possible as it was proven to be a phishing attack, it’s also likely that 2FA could have prevented it as well.
Why Two-Factor Auth?
2FA is not a new concept. It was patented in 1984 by Kenneth P. Weiss and has been slowly gainging popularity throughout the years. One of the first widley adopted methods of 2FA were the card and PIN at ATMs. Now that the need to protect so many digital assets has grown we are struggling to implement it in environments and sofware that may or may not be backwards compatible. As mentioned before however, passwords now are not enough when it comes to the shear amount and sensitive nature of the data we have now in cyberspace.2FA Methods
The different methods of authentication are broken up into three categories- Something you are.
- Biometric (fingerprint)
- Voice
- Something you have.
- Physical token
- Soft token
- Card with magnetic strip
- RFID Card
- Phone (sms/app/phone call)
- Something you know.
- Password
- Passphrase
- Pattern
- Pin
Of course there are many ways that 2FA can fail to be the security blanket that we need, especially when it is implemented poorly. On top of doing your best to increase the complexity of your passwords it needs to be part of your defense in depth strategy and not just a bandaid for a compliance checkmark.
Threats
I’ll give you an example situation that I know for a fact has happened to several pentesters.
Company A decides that they want to implement 2FA by using the push notification or phone call method. A criminal or pentester comes along to break in by either phishing, using passwords from a recent breach, or a password brute forcing technique. Somehow they end up with a legitimate username/password combo, but they should be stopped from authenticating because of the 2FA right? Well in this case, the user gets the phone call or application alert that they have gotten so many times in the past. This notification doesn’t tell the user what they are supposedly logging into, so as a force of habit they acknowledge the alert or answer the phone call and press the # key. Boom the bad guy or pentester is in.
So the principle idea behind “Something you have” can take on different forms. In this situation it’s technically 2FA and allows Company A to be compliant but they are still not leveraging the security potential of the software. If they were to have that second form of authentication include a code as opposed to a single click or button, they would have been both secure AND compliant.
There are many other threats that I won’t get into right now. The bottom line is that passwords alone are weak, and adding 2FA strengthens that authentication method to be a deal more secure. In the words of Bruce Schneier:
“Two-factor authentication isn't our savior. It won't defend against phishing. It's not going to prevent identity theft. It's not going to secure online accounts from fraudulent transactions. It solves the security problems we had ten years ago, not the security problems we have today.”Two-Factor Authentication is just another piece of the security puzzle. It’s not our savior for sure, but it is an essential part of defense in depth.
Friday, August 14, 2015
EMET and You
So first thing’s first. A little explanation of the Enhanced Mitigation Experience Toolkit (EMET) from Microsoft straight from their website:
What is the Enhanced Mitigation Experience Toolkit?
The Enhanced Mitigation Experience Toolkit (EMET) is a utility that helps prevent vulnerabilities in software from being successfully exploited. EMET achieves this goal by using security mitigation technologies. These technologies function as special protections and obstacles that an exploit author must defeat to exploit software vulnerabilities. These security mitigation technologies do not guarantee that vulnerabilities cannot be exploited. However, they work to make exploitation as difficult as possible to perform.
EMET also provides a configurable SSL/TLS certificate pinning feature that is called Certificate Trust. This feature is intended to detect (and stop, with EMET 5.0) man-in-the-middle attacks that are leveraging the public key infrastructure (PKI).
EMET is free, it’s a great tool from Microsoft, and you can go the manual route for installation, or head over to the TrustedSec blog for a post on how to automate it: https://www.trustedsec.com/november-2014/emet-5-1-installation-guide/
A great team member and friend of mine worked closely with me when implementing this technology across approximately 1,500 end devices including Windows 2008 and above, and Windows XP and above. Due to the sensitive nature of our applications, many of which were not stable or secure builds, we opted to perform the installs on our server platforms manually. We worked through a list of about 300 servers performing anywhere from 5-10 installs daily. As we were going through a PC refresh and upgrading everything to Windows 7 at the time we decided to install EMET on our base images after having our application team test the end user software.
From our experiences we encountered few issues, which were easily solved by adding exceptions into our Group Policy.
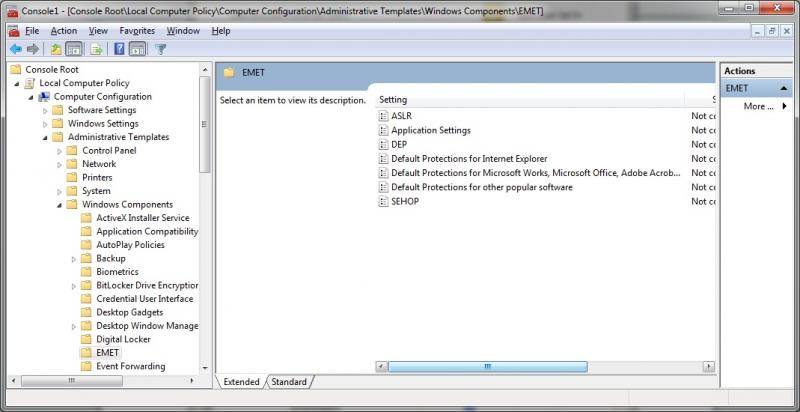
Here is a list of some of the issues that we had encountered. While obviously not a comprehensive one, it will give you an idea of some of the more common pieces of software that we had seen issues with.
With this tool the benefits greatly outweigh the administrative overhead. With a well thought out deployment and the Group Policy to control it. EMET is the icing on your security cake.
What is the Enhanced Mitigation Experience Toolkit?
The Enhanced Mitigation Experience Toolkit (EMET) is a utility that helps prevent vulnerabilities in software from being successfully exploited. EMET achieves this goal by using security mitigation technologies. These technologies function as special protections and obstacles that an exploit author must defeat to exploit software vulnerabilities. These security mitigation technologies do not guarantee that vulnerabilities cannot be exploited. However, they work to make exploitation as difficult as possible to perform.
EMET also provides a configurable SSL/TLS certificate pinning feature that is called Certificate Trust. This feature is intended to detect (and stop, with EMET 5.0) man-in-the-middle attacks that are leveraging the public key infrastructure (PKI).
EMET is free, it’s a great tool from Microsoft, and you can go the manual route for installation, or head over to the TrustedSec blog for a post on how to automate it: https://www.trustedsec.com/november-2014/emet-5-1-installation-guide/
A great team member and friend of mine worked closely with me when implementing this technology across approximately 1,500 end devices including Windows 2008 and above, and Windows XP and above. Due to the sensitive nature of our applications, many of which were not stable or secure builds, we opted to perform the installs on our server platforms manually. We worked through a list of about 300 servers performing anywhere from 5-10 installs daily. As we were going through a PC refresh and upgrading everything to Windows 7 at the time we decided to install EMET on our base images after having our application team test the end user software.
From our experiences we encountered few issues, which were easily solved by adding exceptions into our Group Policy.
Here is a list of some of the issues that we had encountered. While obviously not a comprehensive one, it will give you an idea of some of the more common pieces of software that we had seen issues with.
- EMET with EAF battles Adobe Reader (All versions)
- There is a known issue with EMET’s caller mitigation in Chromium since v34 (http://www.chromium.org/Home/chromium-security/chromium-and-emet). Microsoft and the devs both say that there is no benefit to leaving EMET Caller mitigation turned on for chrome.exe. They also recommend turning off SEHOP mitigation for chrome.
- Msaccess.exe has to be allowed in both DEP and Caller.
- Photoshop.exe has to be allowed in DEP.
With this tool the benefits greatly outweigh the administrative overhead. With a well thought out deployment and the Group Policy to control it. EMET is the icing on your security cake.
Subscribe to:
Posts (Atom)




